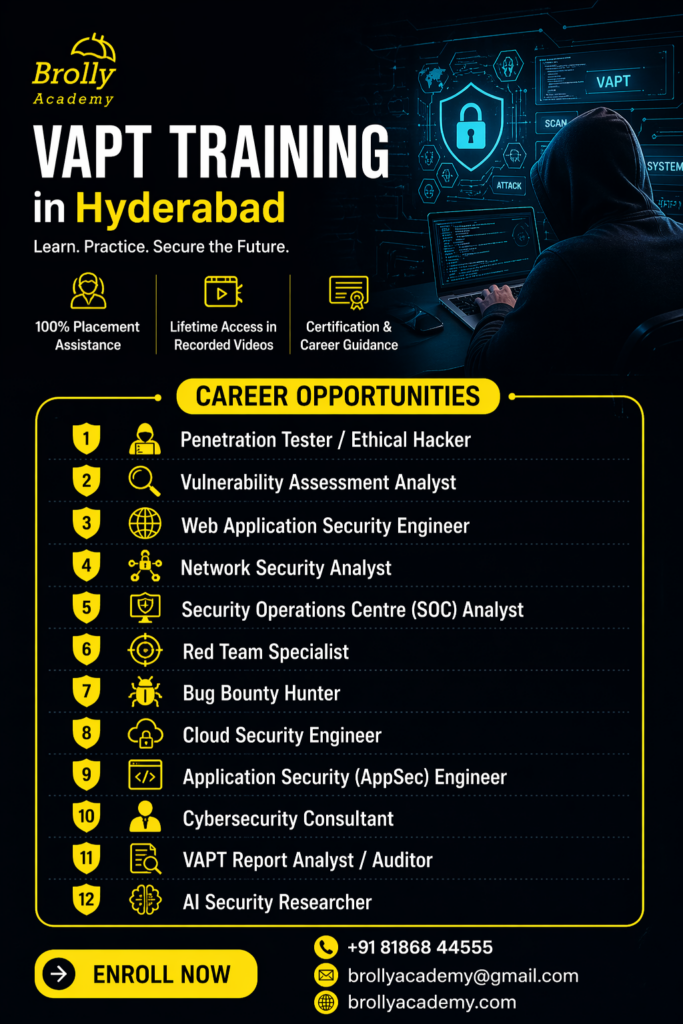
VAPT Training in Hyderabad
with
Certification & 100% Placement Assistance
Classroom course | Online course | Capstone Projects | 2–3 Months | Flexible EMI | Free Demo Class
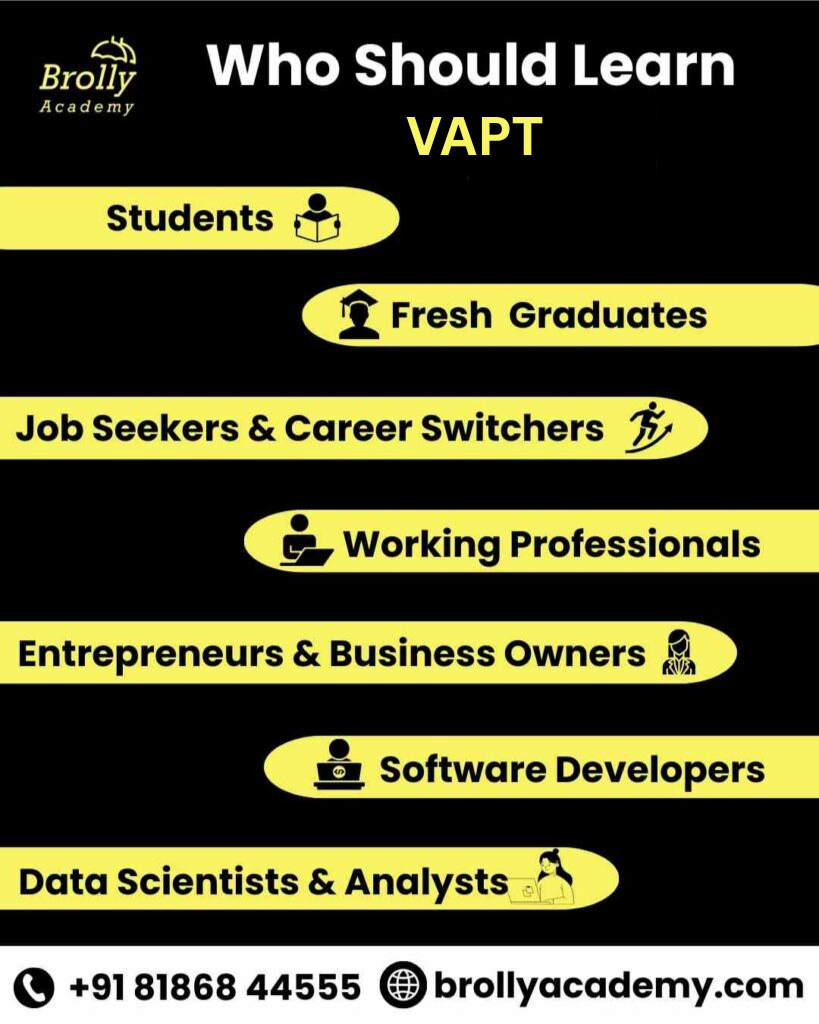
Looking for the best VAPT training in Hyderabad? Our comprehensive penetration testing course in Hyderabad is designed for aspiring ethical hackers, security analysts, and cybersecurity professionals who are ready to break into one of India’s fastest-growing IT fields. Our curriculum encompasses the entire VAPT lifecycle — from reconnaissance and vulnerability scanning to exploitation, post-exploitation, and comprehensive security reporting.
You will gain hands-on expertise with industry-standard tools, including Kali Linux, Burp Suite, Metasploit, Nmap, Wireshark, and OWASP ZAP, guided by certified trainers with 10+ years of real-world cybersecurity and ethical hacking experience. Whether you are a fresh graduate, IT professional, or career switcher, our cybersecurity training in Hyderabad prepares you for top certifications like CEH, OSCP, and CompTIA Security+, along with live project exposure and 100% placement support.